In today's interconnected world, safeguarding your digital assets is paramount. Implementing robust access control measures is crucial for mitigating unauthorized entry. By carefully regulating user permissions and privileges, you can create a secure environment that protects your valuable information.
- Employ strong authentication methods, such as multi-factor authentication, to verify user identities.
- Deploy role-based access control (RBAC) to grant users privileges based on their job functions.
- Audit system activity logs to detect any suspicious actions.{
By integrating a comprehensive access control strategy, you can strengthen your digital defenses and minimize the risk of security incidents.
Unlocking iPhone Access Control Settings
iPhone access control settings are a crucial aspect of safeguarding your privacy and sensitive information. By adjusting these settings, you can effectively manage who has permission to your device and its data.
Start by exploring the in-depth range of options available in your iPhone's Preferences app. Here, you can configure strong passwords, enable Face ID or Touch ID for fingerprint authentication, and limit access to certain apps and features.
Remember to regularly review your access control settings to ensure maintain a high level of security. By keeping up about the latest security practices, you can effectively strengthen your iPhone's defenses.
Bolstering Security with Robust Access Control Systems
Access control systems are vital in safeguarding sensitive information and ensuring the security of your infrastructure. Robust access control goes beyond standard authentication methods, implementing multi-factor authentication and granular authorizations to mitigate risks. By rigorously controlling who has access to what, organizations can effectively minimize the likelihood of unauthorized access, data breaches, and other security vulnerabilities.
A comprehensive access control system should include a range of elements to provide a layered defense. This may encompass centralized user management, role-based access control (RBAC), auditing functions, and data protection. Regularly assessing your access control policies and procedures is essential to ensure they remain effective against evolving threats.
Strategically investing in a robust access control system demonstrates a commitment to security, protecting your valuable assets and maintaining the trust of your customers.
Control de Acceso para Dispositivos Móviles
El acceso a los dispositivos móviles es una aspecto crucial en la era digital. Los usuarios generan y almacenan gran cantidad de información sensible en sus teléfonos inteligentes y tabletas, haciéndolos exponibles a las ataques cibernéticas. Implementación de mecanismos de control de acceso robusto es esencial para evitar estos riesgos y garantizar la privacidad de los datos.
Un sistema efectivo de protección de acceso para dispositivos móviles debe incluir medidas como:
* Códigos fuertes y complejas
* Bloqueo del dispositivo después de un número determinado de intentos fallidos.
* Aplicaciones de seguridad móviles que ofrecen funcionalidades como el detección de malware y la protección contra ataques.
Alcanzar una seguridad sólida requiere de una estrategia integral que involucre tanto al usuario como al administrador del dispositivo.
Comprehending Access Control Mechanisms
Access control mechanisms represent fundamental components within any secure system. Their core purpose is to control access to resources, ensuring that only approved users or processes can interact them. These mechanisms implement various methods to validate user identities and bestow appropriate permissions based on their roles and responsibilities. A robust access control system can minimize the risk of unauthorized infiltration, safeguarding sensitive data and maintaining the integrity of the system as a whole.
Adjusting Access Control for Optimal Protection
In today's dynamic cybersecurity landscape, organizations must/need to/have to constantly evaluate/assess/analyze their access control mechanisms/strategies/policies. A well-defined access control framework/system/structure is essential/crucial/critical for mitigating/reducing/preventing the risk of unauthorized access and data breaches. However, a static approach to access control can be ineffective/vulnerable/susceptible in the face of evolving threats and business requirements.
Therefore, organizations should/ought to/must implement/adopt/integrate a proactive/dynamic/adaptive strategy for fine-tuning access control. This involves regularly/periodically/continuously reviewing/assessing/auditing access permissions, identifying/detecting/uncovering potential vulnerabilities, and implementing/applying/enforcing appropriate/suitable/relevant controls to ensure that only authorized users have access to the resources they require/need/demand.
A robust fine-tuning process should/must/ought to incorporate/include/comprise several key elements/components/factors. First, it is important/essential/critical to establish clear roles and responsibilities for access management. This entails/includes/requires defining user roles based on their functions/duties/responsibilities and assigning appropriate permissions accordingly/consequently/therefore.
Furthermore/Moreover/Additionally, it is crucial to implement/establish/deploy strong authentication mechanisms, such as multi-factor authentication, to verify user identities and prevent unauthorized access.
Security information and event management (SIEM) systems control de acceso a edificios públicos can be valuable/beneficial/helpful in monitoring user activity and detecting suspicious behavior. Regular security awareness training for employees is also essential to raise their awareness/knowledge/understanding of cybersecurity best practices and promote a culture of security.
By implementing/adopting/integrating a comprehensive fine-tuning strategy, organizations can enhance/strengthen/fortify their access control measures and effectively protect their sensitive information from unauthorized access and cyber threats.
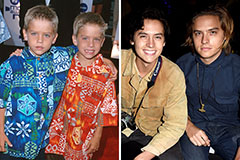 Dylan and Cole Sprouse Then & Now!
Dylan and Cole Sprouse Then & Now! Tahj Mowry Then & Now!
Tahj Mowry Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now! Lisa Whelchel Then & Now!
Lisa Whelchel Then & Now! Atticus Shaffer Then & Now!
Atticus Shaffer Then & Now!